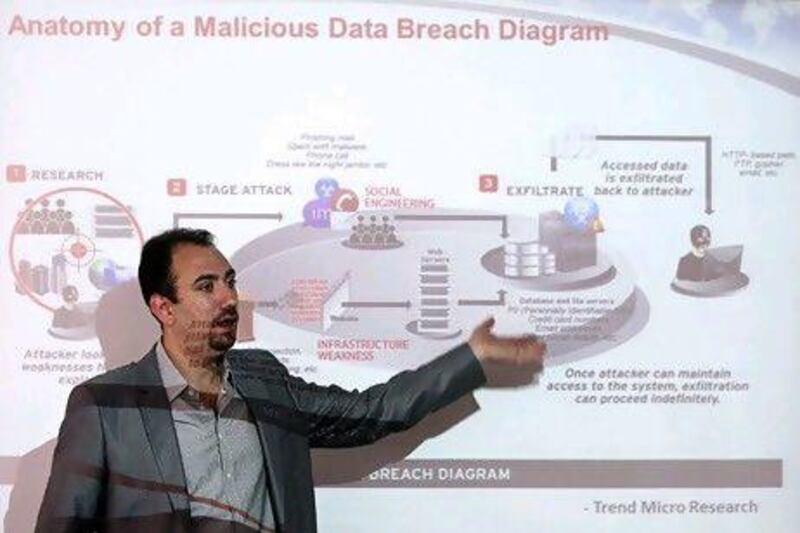
On a sunny Tuesday morning last month, Alaa Kharfan was sitting at his laptop, scrolling down a list of possible cyberattacks he could unleash.
After dismissing a "spear-phishing attack", as well as a run-of-the-mill website-cloning scam, he settled on a social-engineering attack.
But Mr Kharfan is not a hacker. He is a senior sales engineer with Trend Micro, a global computer security company with a branch in Dubai. And he was demonstrating during a workshop just how easy it is to hack a computer using a tool that is easy to find online and free to download.
The programme, which is designed to help IT administrators check the vulnerabilities of a network, includes a list of commands that take people step-by-step through the process of hacking into a computer.
"They have a kit for social engineering," says Mr Kharfan.
This week, Gulf Air from Bahrain posted a notice online advising its customers that its official Facebook page had been hacked.
"Right now, the page is not under our control, so kindly ignore any messages, videos or pictures that may be posted," the airline warned.
Estimates for the prevalence of cyberattacks in the UAE range widely.
One hundred phishing attacks were registered in the Emirates last year, with 72 of them conducted against banks, according to aeCERT, an agency tasked with overseeing internet security in the country.
But IT Matrix, an online anti-fraud company, said it detected 1,145 unique phishing attacks in the UAE in 2010, the most in the Arab world.
Some cybercriminals use "bots" to perform automated tasks such as sending spam emails.
"If you want to bring down a website, you fire up these machines and get them to send a mail bomb to a specific website," says Nick Black, the senior technical manager with Trend Micro.
That means spam is more than just irritating. "It is really the vehicle to deliver malicious content," says Mr Black.
One spam emailpurporting to be from the social-networking site Facebook recently urged people to follow a link and update their accounts. It prompted them unwittingly to install a Trojan horse virus designed to steal bank account details.
Digital security companies may not be quick to advertise this to consumers, and antivirus software will not always pick up the problem.
Even spam that claims to include a link to a website that turns out to be a harmless-looking advertisement can be more sinister than it appears.
Some spam emails of this type include malicious computer code that gives cybercriminals permission to access a computer to steal information or even capture video footage of the user through his or her own camera.
But the most frightening part may be how easy it is to hack into someone's computer.
Last year, a hacker infiltrated the US-based computer security firm RSA. The hacker sent out an email called "2011 Recruitment Plan" that was automatically marked as junk. That fooled an RSA employee into opening it, thereby installing a virus in the company's network, allowing the hacker to do anything remotely that employees could do locally.
Back in Dubai last month, Mr Kharfan cloned a Facebook log-in page during his workshop. The cloned page was used as a link in a message saying "please check this out on Facebook".
Those who followed the link would enter their log-in details, which then appeared in the programme Mr Kharfan was using.
In the UAE, organisations such as aeCERT work to raise security awareness, "a never-ending exercise", says Ahmad Hassan, who heads research and analysis at aeCERT.
So how can people best protect themselves?
Strong passwords are a must, Mr Hassan advises.
"Another method is the use of antivirus [software] and regularly updating it," he suggests. "New viruses are developed all the time."
And people should always install the latest security updates and patches to their operating systems and programmes.
"These updates fix weak points in the computers that the hackers make use of to perform their attacks," he says.
twitter: Follow our breaking business news and retweet to your followers. Follow us